How to Hack iPhone Messages for Free [UPDATED]
Like all people today, you are probably worried about the things your spouse or business partner discusses with your foes. It’s good you are concerned because there are more threats out there relating to tech and communication than you would expect.
Fortunately, this guide sheds light on one of the best ways for how to hack iPhone text messages.
Ready to get informed? Let us dive right into it!
How to Hack Someone’s iMessage Without Them Knowing?
Based on our experience, there are various ways to hack someone’s iMessage without them knowing. Usually, it involves the use of a mobile application, and the common ones include:
SpyBubble
SpyBubble is a powerful monitoring tool that allows you to access various types of data on a target device. The app offers a range of features, including:
Text Message Monitoring
Our investigation shows that SpyBubble provides a reliable solution for monitoring text messages. With this app, you can easily access and view all incoming and outgoing text messages on the target phone, even deleted ones.
Call Log Tracking
Stay informed about who your target contacts regularly by using SpyBubble’s call log tracking feature. This feature provides detailed and organized information about all incoming and outgoing calls, allowing you to monitor your target’s communication patterns.
Media File Viewing
Concerned about inappropriate content being shared or received on the target device? SpyBubble allows you to view any shared media files, such as photos and videos, giving you real-time insights into your target’s multimedia activities.
Browser History Monitoring
Worried about your target’s online activities? SpyBubble enables you to monitor their browsing history by providing access to website descriptions, timestamps, and URLs. This feature helps you gain a better understanding of their online behavior.
SIM Card Information
With SpyBubble, you can stay one step ahead of your target’s attempts to hide their activities. The app provides essential information about SIM card swaps, including network carrier details, IMEI numbers, and other important information.
Based on our observations, SpyBubble is a comprehensive monitoring solution that offers valuable insights into the activities of your target. It provides a range of features designed to help you keep an eye on their digital behavior and ensure their safety.
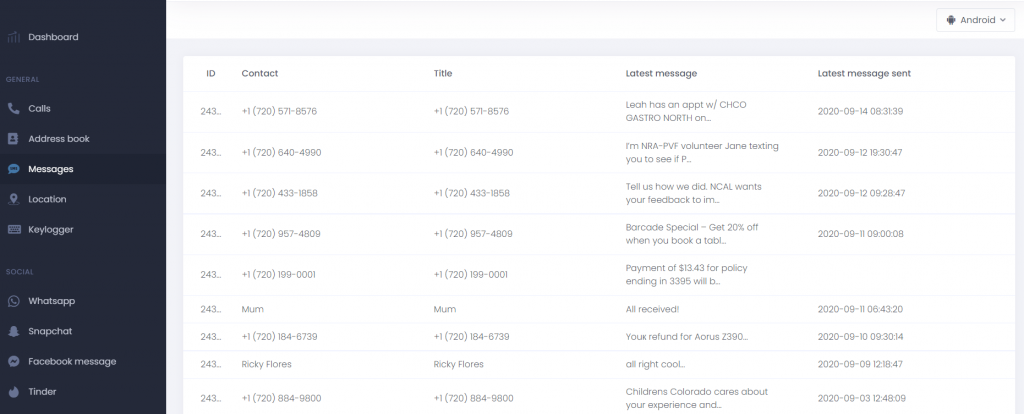
mSpy
mSpy is a brand of computer and mobile software that works on various device platforms. It can work on platforms such as iOS, Windows, Android, and macOS. According to our experience, this iMessage hack app is an excellent bet. The software is robust, and includes the following features:
Message Tracking
The app can track messages that the given iPhone sends through local network providers. mSpy can also track messages sent through mobile applications like spying on Whatsapp
Keylogger
mSpy is also capable of tracking the keyboard queries that the phone users type into search engines or mobile applications. It then gives you access to this information in the form of a concise list.
Screen Recording
The app also lets you record user sessions or activities through this function. You can then access the content in the form of a video containing the details on phone usage.
Location tracking you also get real-time information on the location details of the phone user.
WhatsApp and Facebook Monitoring
You can also use the mSpy app to track the instant messages and calls that occur through WhatsApp. Since most people conduct communications through social media, mSpy has a handy function to let you access such data.
How to Install mSpy
The steps involved in setting up mSpy are simple, but you may have to consider a few requirements.
Requirements:
- Needs physical access to the device, supports stealth mode, and installation is required directly to the phone. iOS users can install the app remotely if they have the target’s iCloud credentials.
Steps
- Visit the mSpy website with your preferred device, and create a user account.
- Next login to your account, and pick a suitable subscription plan.
- Prepare your Android or iOS device for app installation.
- Install the app, and start monitoring.
uMobix
uMobix is a iPhone tracking mobile software solution that specializes in tracking your kid’s usage activities. Many users find the app useful for how to hack iPhone. Thanks to the app’s highly intuitive design, it’s easy to see why uMobix guarantees a fun user experience. Based on our own experience, this Android and iPhone spying app supports various functions including:
Access Controls
The app provides you with access to the main settings on your child’s phone or tablet. You get the freedom to access some of the phone functions, which is important in restricting access to the internet. Plus, the access controls are also customizable to suit your monitoring needs.
Location Tracking
The app features a specialized GPS tracker, and a thorough map to help track your little one’s movements. However, you have to activate the “Location Tracking” feature first for the app to start uploading the data.
Call Tracking
You can gain lots of insight from the people your child interacts with through phone calls. uMobix lets you leverage this feature by helping you track all call activity that occurs on the given device.
Keylogger
With uMobix, you also get the ability to track the specific login details and queries your little types on their phone. The app then presents this information in a well-organized list.
Access to Deleted Messages
While your little one might be clever in the ways, and delete some of received text messages, before you can access them, uMobix can solve this problem. That is because the app lets you access any deleted messages conveniently.
Access to Social Apps
Your child is probably active on platforms such as Instagram and Twitter. However, it’s not easy to access their social media profiles, especially as they tend to conceal some of their activities. uMobix lets you access the content that your child accesses and shares through social apps.
Can Someone Hack My iPhone Text Messages for Free?
Yes, someone can hack your iPhone text messages for free. Below are the common techniques they are likely to use:
Zero-click Attack
Refers to a remote cyberattack that does not require physical access to your device. Usually, the attack involves illegal access to the device, without the target clicking on any application or website.
While the attack is less likely to occur, a recent report by Wired showed the ways state agencies misused it to access devices. It involves an orchestrated attack by the Bahraini government on its citizens.
The Zero click attack does well to portray the many vulnerabilities that exist in most devices today. Some malicious individuals are willing to go to great lengths to find these vulnerabilities.
Lock Screen Bypass
Your phone is also prone to the famous lock screen bypass, which circumvents the basic security controls on your iPhone device. While the basic iPhone security functions are difficult to crack, the lock screen bypass method takes on many forms. It’s one of the best ways for how to hack iPhone text messages.
Furthermore, the specific lock screen bypass method that will work for your phone depends on the iOS version you are using. For iOS 8 to 10.1, you can bypass the lock screen with the help of Siri.
It’s an in-depth process and this guide should be helpful.
How to Hack Someone’s iPhone Texts Using Kali Linux
Kali Linux refers to an open-source operating system that many hackers use today. It provides users with access to over 600 penetration tools and security data. Users can easily tweak the code to suit specific device phone hacking applications.
For iPhone hacking, the process involves several coding steps and procedures. Furthermore, most hackers use penetrations tools such as Nmap and Lynis, which can often seek to find security vulnerabilities.
Lock Screen Bypass
Your phone is also prone to the famous lock screen bypass, which circumvents the basic security controls on your iPhone device. While the basic iPhone security functions are difficult to crack, the lock screen bypass method takes on many forms. It’s one of the best ways for how to hack iPhone text messages.
Furthermore, the specific lock screen bypass method that will work for your phone depends on the iOS version you are using. For iOS 8 to 10.1, you can bypass the lock screen with the help of Siri.
It’s an in-depth process and this guide should be helpful.
How to Hack Someone’s iPhone Texts Using Kali Linux
Kali Linux refers to an open-source operating system that many hackers use today. It provides users with access to over 600 penetration tools and security data. Users can easily tweak the code to suit specific device phone hacking applications.
For iPhone hacking, the process involves several coding steps and procedures. Furthermore, most hackers use penetrations tools such as Nmap and Lynis, which can often seek to find security vulnerabilities.
Online iPhone Hacking Tools
There are various tools you can use to hack iPhone text messages online. Usually, these tools are in the form of downloadable software or an I.T service, which you can access based on a paid subscription. However, the sad fact is that most of these websites are fake and want to trick users into downloading malware on their devices.
NOTE: While the techniques mentioned are excellent for hacking iPhone messages, they require advanced programming techniques. It’s close to impossible for the average person to orchestrate these iPhone text messaging hack techniques. Also, stay clear of ”free hacking websites” because you’ll end up contracting malware on your macOS or iPhone.
Can iPhone Be Hacked Through Texts?
Technically, nobody can hack an iPhone through texts. However, it’s possible through the use of resources such as third-party apps. These refer to apps that you install on a phone, usually after performing a jailbreaking process. We recommend SpyBubble as the best choice.
If you are still doubtful about how to hack an iPhone to read text messages, realize that you may have to use different techniques. You may have to hail break the phone to ensure the device can support the iPhone text message hacker software.
Can You Hack iPhone Text Messages Remotely?
No, you cannot hack iPhone text messages remotely. That is because iOS contains several security controls and functions to stop iPhone hack texts. These security measures are almost impossible to bypass using traditional device hacking techniques.
However, your best bet at hacking an iPhone text message remotely would be to use a reputable spy app. While some of these apps require jailbreaking to function, they will give you real-time access to the SMS content on the device.
Conclusion
The iPhone brand ranks among some of the best and most secure flagship devices in the world today. This means that they design most of their software and hardware resources to function optimally. So, hacking iPhone messages for free will be a significant challenge, especially if you not well informed. However, it’s possible when you have access to the right tools and information. The easiest way to achieve this goal is to use iPhone message hacking software like SpyBubble.


Angelica
When I’m not at work, you’re most likely to find me grabbing a coffee and indulging in a gripping and well-written piece of crime fiction. Alternatively, you could find me rallying for my kids at their soccer matches.
A self-proclaimed expert in cybersecurity. I regularly test and review parental monitoring software, so you can make an informed decision about which ones deserve your money and which ones you should ignore.
Angelica posts:
How to Track Your Boyfriend Without Him Knowing for Free
Can Someone Track Your Location From a Text
How To Put a Tracker on a Phone
uMobix Review